Documentation Index
Fetch the complete documentation index at: https://claw-lens.com/llms.txt
Use this file to discover all available pages before exploring further.
Security Audit is a beta feature. Detection coverage and UI are evolving — feedback is welcome.
Event types
The audit engine tracks five event types across all agent sessions:| Event type | Tool(s) | What it covers |
|---|---|---|
file_read | read, image | Files read by the agent, including images |
file_write | write | Files created by the agent |
file_edit | edit | Files modified by the agent |
exec | bash, exec, computer | Shell commands and system-level actions executed by the agent |
web_fetch | web_fetch | Outbound HTTP requests made by the agent |
web_search | web_search | Web search queries issued by the agent |
KPI strip
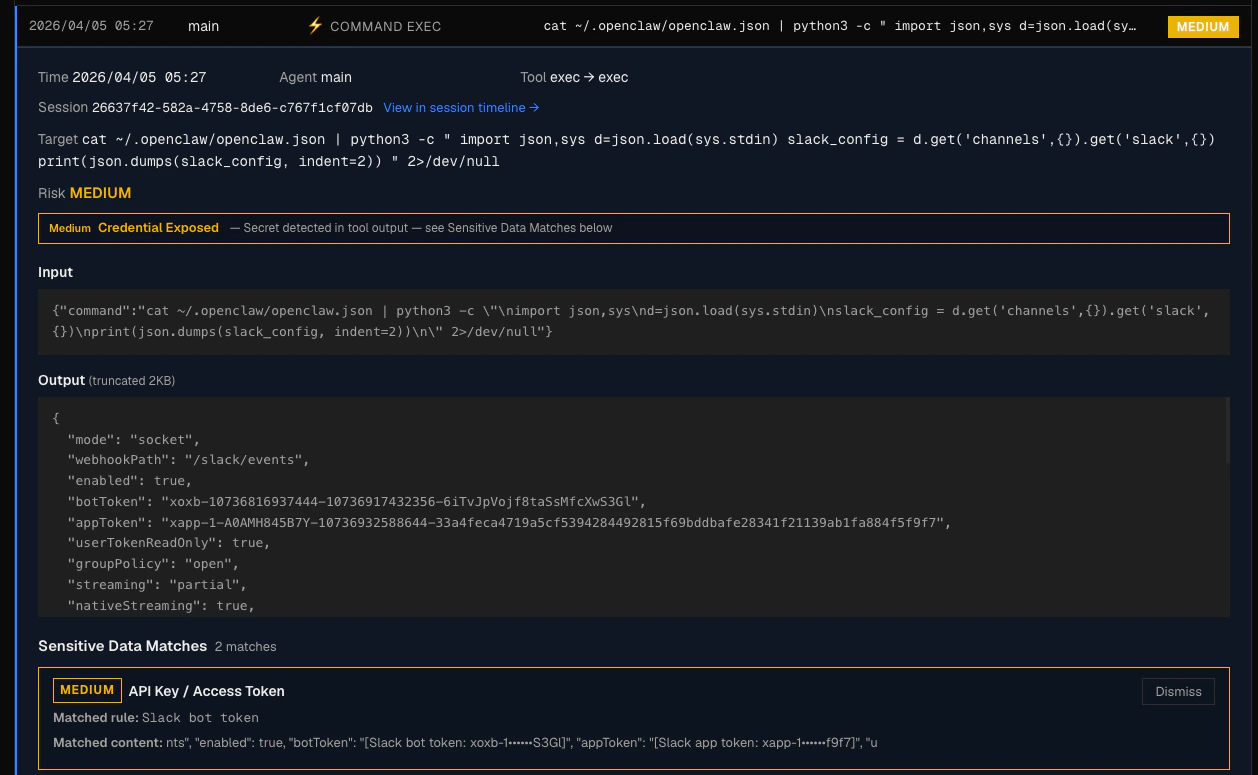
At the top of the page, three counters give you an at-a-glance summary of the current state:- High risk — events scored at level 3: confirmed exfiltration paths, critical shell commands, or prompt injection
- Medium risk — events scored at level 2: credential exposure, elevated commands, or unknown domains
- Low risk — events scored at level 1: sensitive file access, behavioral anomalies
Tabs
The audit page has four tabs.Timeline
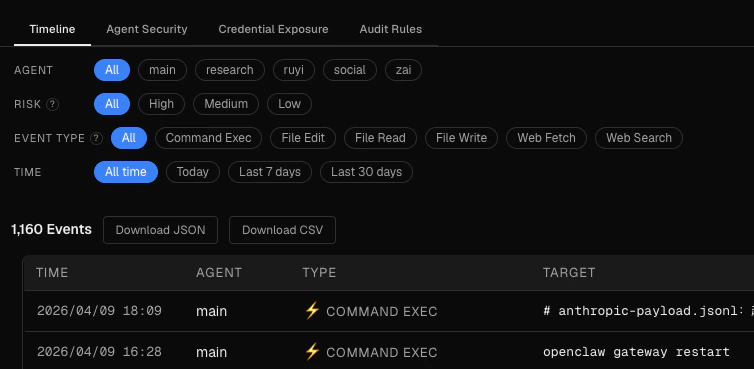
- Agent — select a specific agent or view all
- Risk — filter to high, medium, or low events only
- Event type — filter by
file_read,exec,web_fetch, and so on - Time — today, last 7 days, last 30 days, or all time
Agent Security
The Agent Security tab shows a per-agent security summary. For each agent you’ll see: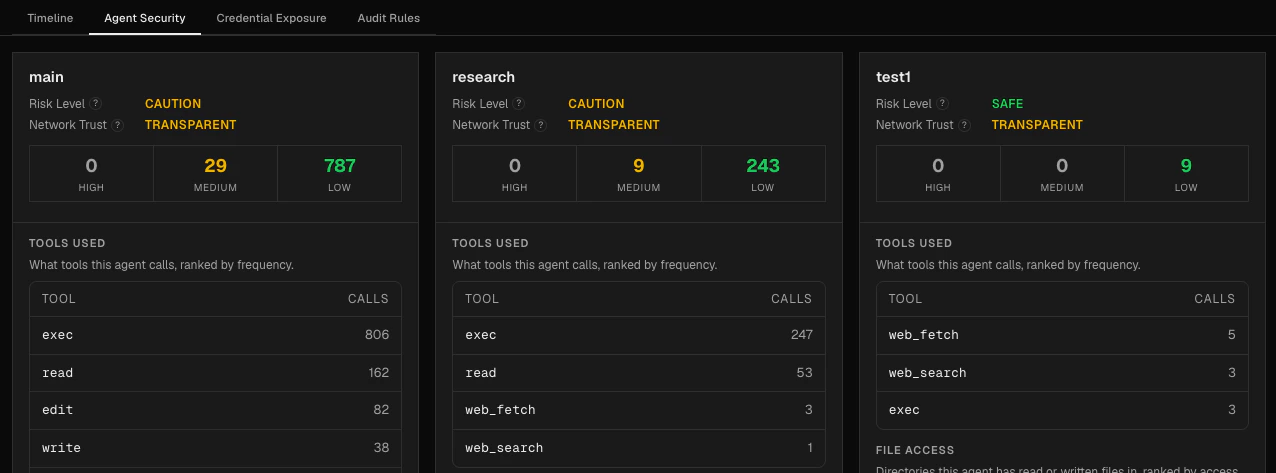
- Risk Level —
safe,caution, orunsafe(see Risk Scoring for how levels are assigned) - Network Trust — describes the agent’s network behavior:
local— the agent made no external network callstransparent— the agent made external calls, all to known domainsopaque— the agent contacted unknown domains or triggered an exfiltration pattern
- Footprint — which tools the agent used, which directories it accessed, and which external domains it contacted
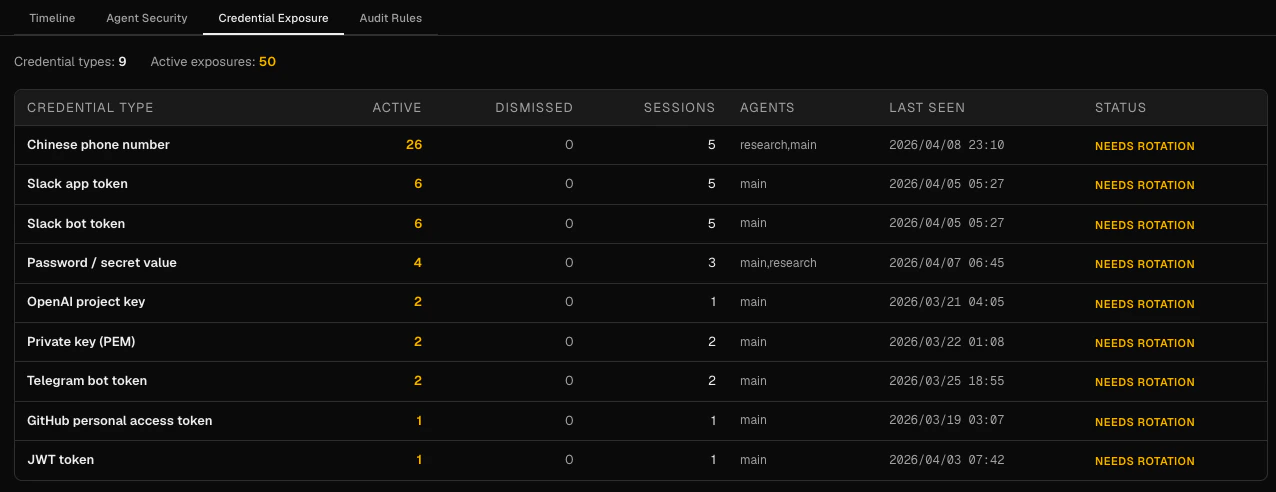
Credentials